This is the second half of the article which I published last week. I have been overwhelmed with the positive responses to the first article, so I’ll take this opportunity to say thank you very much for your kind words. I’m glad that the article was useful for so many of you, and I hope you get just as much out of this edition.
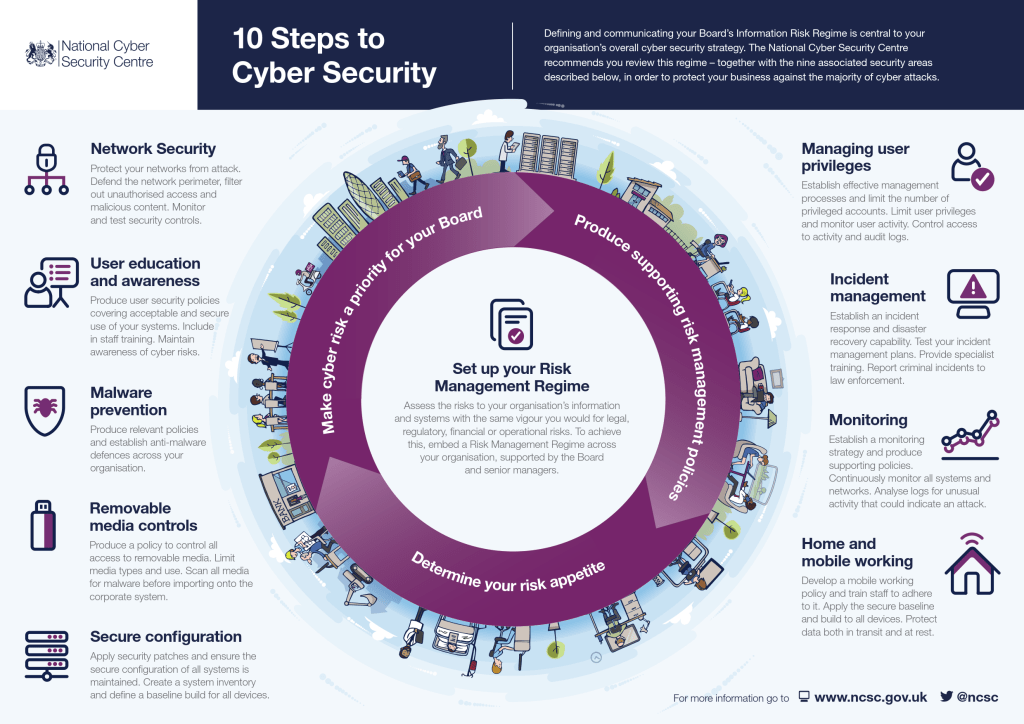
This article covers the remaining aspects of the UK Government’s 10 Steps to Cyber Security, and is again aimed at those of you with limited or no cyber / information security awareness. Again my aim is to explain the requirements in a simple manner with no jargon or buzzwords. As last week covered steps 1 to 5, this week we start at 6…
6. The first step we’ll look at in this article is all about User Education and Awareness. Yes, training is a very important part of our controls and which help protect our businesses. It forms a part of many regulatory frameworks, but we shouldn’t just do it because the regulations or contracts we work to require it.
Within the 10 Steps, the guidance suggests that once you’ve produced all your policies and processes you ensure that those are described within the training you provide. It helps to maintain awareness of cyber risks, and at the very least should mean that all staff are aware of what is expected of them.
Many companies have for years run this as a kind of “tick box” exercise, where people simply rush to the end as fast as possible just so they can say they’ve completed it for another year. That adds no value. The employee gains nothing and the business is not better protected – but it may be sufficient to meet our regulatory, legal or contractual obligations.
Good awareness training should help to inform and change behaviour, to make it easier for people to do the right thing than the wrong thing. It should help explain the risks of certain actions in a way that matters and affects the individual: it should explain the “what’s in it for me” question. Humans are the weakest link in any security solution, so we should help them get it right by helping them understand what’s at stake. Many good training solutions now include gamification, or “what would you do” type scenarios. Get the attendees actively involved in the training, rather than passively clicking “Next” to get to the next screen.
7. Managing User Privileges is the next step. This simply means restricting access to the highest privilege type of account to as few people as possible. You should also monitor user activity if possible, looking out in particular for unusual activity such as logging in at strange times of the day, or for large file transfers out of your business. This also involves looking at audit logs, which you may need help with.
User accounts on most computers fall into two areas: administrator (also known as admin, superuser, root, or something like that) and standard user.
The standard user cannot run new programs, cannot install software on their machine etc, because their access rights (another way of saying user privileges) don’t give them carte blanche access to the device.
The administrator account has full access to be able to run any software, to remove components, and to run administrative tools such as reformatting drives. This is very powerful and, as a result, users with this level of access should be restricted as much as possible.
It is good practice to give most users standard user accounts, because for the most part they should not need to install software or make significant changes to their machines. It’s also good practice to review who has what level of access on a regular basis, and make sure that people only have access to systems and data that they need for their job. For example, someone working in a technical team doesn’t need access to payroll data, and someone working in HR doesn’t generally need to be able to install new software on a server.
8. The next step is Incident Management. This is not only about how you deal with an incident when it occurs, but about being prepared for one when it happens. (Notice that I’ve said “when” rather than “if”. Statistically, if you’ve not had an incident then you will soon, so it helps to be prepared.) The key areas to bear in mind are:
- Ensure that you have a documented incident response process, that you know what to do and who to contact. For example, where would you relocate your business / staff to if your offices were unavailable due to fire, flood or a chemical spill? How would you contact staff to tell them where to go and when? Are all staff required or just one or two? What equipment will they need and how would they access your systems? If you’re using a shared recovery office, how are you guaranteed space? What would you do if your office systems were infected by ransomware? This is the sort of thing that should be considered and the processes documented. This is all part of something called Business Continuity or Disaster Recovery Planning.
- Once you’ve got your plans in place, test them. You should aim to test them at least once a year. Some companies do a full test where they actively notify people and try running their business from the recovery offices for a day, and some run a table top exercise. Both work, and both have their risks and benefits.
- Just as your business will likely have fire marshalls, first aiders and health and safety experts, make sure staff are trained in what to do in the event of an incident. The training doesn’t have to be onerous and many businesses will include it as part of their User Education and Awareness activities described in 6 above.
Where you find a criminal incident, it should be reported to law enforcement via Action Fraud – http://www.actionfraud.police.uk. You may also choose to inform your local police force.
9. The penultimate step is Monitoring. As we’ve seen, there is some overlap with step 7, but monitoring covers more than just user account management. There are a couple of things to look at when dealing with this step:
- You should establish a strategy for monitoring, and document this – ideally include it in your overall Information Security Policy. Monitoring may also include email and internet use as well as systems and networks: if it does, then you need to make your staff aware that this is the case.
- Monitoring of systems and networks should be continuous, so you’ll need a way of identifying anomalies / unusual behaviour. This may be through log analysis or you may look for software which helps to visualise the data, which make the anomalies stand out.
- Though the guidance doesn’t specifically mention it, I’d suggest that your monitoring should also include details around key indicators, change management etc. For example, if you have a policy that requires all laptops to be encrypted, then you should check regularly to ensure that they are and report on those that aren’t. Or if you have a policy of removing user access when they leave the organisation, you should check to ensure that is happening on a regular basis.
10. Finally, Home and Mobile Working is an area that you need to look at.
- Make sure that your Information Security Policy includes a section on mobile working. Do you allow it or not? If you do allow it, what are the rules, how is data protected? Do you allow users to use their own devices, or do you provide laptops, tablets, smartphones etc. What security is in place to protect the data, both at rest and in transit (ie when being sent across networks – do you use Virtual Private Networks, encryption, two factor authentication etc)? Make sure you’ve documented what your security baseline is and ensure that is being complied with through regular monitoring as discussed in step 9.
- Make sure that users know what is and isn’t allowed, what is acceptable behaviour and what is expected for them if they are working from home or on the road. This is a great topic to include in step 6, your User Education and Awareness.
As you can see, these steps are relatively straightforward, and there is a degree of overlap between them. For the most part it all boils down to how you protect your data, how you ensure the data cannot be tampered with, and how you get access to it in the event of an incident. In Information Security terms, this is known as the CIA triad, Confidentiality, Integrity and Availability. Make sure you’ve documented your requirements and communicated them with staff on a regular basis, and review your requirements regularly too.
Are there any areas I’ve not explained well? I’m happy to answer any questions you may have so please just ask!
Leave a comment